Recovering your Windows XP computer from a Virus, Worm, Adware, Spyware or Browser Hijack Infection
Summary
Important: Instead of spending valuable time trying to
determine exactly how your computer is compromisedùvirus, worm, adware,
spyware or browser hijackùthe following steps will address
each of these possible infections in turn.á
Since your computer could be a victim of several types of infection,
please follow these steps in the order they are listedùeven if you think you
know what type of infection you have.á
This is the best way to make sure your computer is recovered completely
from one or more of these types of infections.á
Note:
To do the following steps be sure you are logged into your computer on the
account that has administrator privileges.á If your Windows
XP computer has only one login (or you donÆt have to log in at all)
then you are the administrator.á If your
computer has multiple loginsùone for each member of the family, or it is a work
computer on a domain, then be sure to login on the account that has administrator
privileges before doing the following steps.
Initial Preparationùdisconnect your computer
from your network
╖
Before turning your
computer on
1. Unplug any network cables.
2. If your computer is setup to connect to a wireless
network, make sure your wireless router is turned off prior to
turning on your computer.á
3. When you are sure that your computer is disconnected
from any network, turn it on and proceed to the next step.
Do a full Virus and Worm scan
╖
Immediately after
turning your computer onùdo a full virus and
worm scan
To
do a virus/worm scan of your computer you must have an antivirus program
installed, like Norton Antivirus
or McAfee Virus Scan.á
Follow these steps, depending upon your situation:
╖
If you have an
antivirus program installed
1. Perform a complete virus scan of your computer.
2. If infected files are found, follow the prompting of
your antivirus software to remove them.á
Keep rescanning your system until it comes up clean, then reboot it and
scan it again to be sure it is still clean.á
╖
If you do not
have an antivirus program installed
1. Purchase an antivirus program immediately.á We recommend either Norton
Antivirus or McAfee Virus Scan.á
Important:
Most antivirus applications come with the ability to scan and remove viruses
from your computer prior to installing themùinstalling any
application on a computer infected with a virus can corrupt that application so
that it will not work. Before installing your antivirus application, follow the
instructions that come with it and scan and clean your system.
Do a full Adware/Spyware scan
╖
After you scan for
virusesùdo a full adware/spyware scan
To do an adware/spyware scan
of your computer we recommend using both Ad-Aware and the Microsoft
Windows Defender.á Follow these
steps to install both programsùreconnect your computer to the internet to do
this.á Note: If you are unable to navigate
to the following websites to download these applications your browser may be
hijacked.á In that case, proceed directly
to the
Recovering from a Browser Hijack section below.
Installing and running the Microsoft Windows Defender:
1. Open Internet Explorer and go to www.microsoft.com.á At the bottom of that webpage is a Popular Downloads section.á Click on the Microsoft Windows Defender item there. Or click this link.
2. Follow the steps to install the Microsoft Windows Defender program.
3. After the installation is complete, run the Microsoft Windows Defender program and have it scan your computer.á Follow any on-screen prompts to remove any adware and spyware that is found.
4. Reboot your computer and run the Microsoft Windows Defender program
again.á When the scan finally comes up
cleanùyou may have to repeat step 3 several timesùproceed to the ôInstalling
and running the Lavasoft Ad-Aware programö below.á Important: If an adware/spyware item that was
detected and removed in a previous scan keeps reappearing in the list of found
items, it is most likely the result of a registry
key that has had its security modified so that it cannot be deleted by the Microsoft Windows
Defender program.
Note: The Registry on your computer is like the book catalog in a library
where information about all the books in the library and where to find them is
listed.á In a similar way, the registry
contains an entry for each of the programs installed on your computer.á When Adware or Spyware infects your computer
they make entries for themselves in your registry. Microsoft Windows Defender tries to remove
these bogus entries. If you have one or more of these entries that keep coming back
after each scan, you will need to delete them manually by following these
steps:
Manually deleting an Adware/Spyware
Registry Key
Carefully
follow these steps to manually delete the adware/spyware registry keys that the
Microsoft Windows
Defender program cannot:
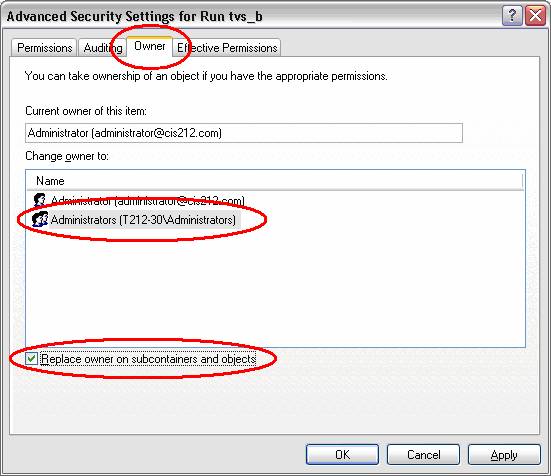
a) To find the location and registry key name of the
adware/spyware items while they are listed in Microsoft Windows Defender, click
the little + button below the
spyware name. The following illustration is an example of an adware registry
key entry as displayed in the Microsoft Windows Defender program:
![]()
Write down
the full registry key path of the offending registry key entry. In the example
illustration above, that would be:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
tvs_bá
In the above example, the
adware registry key name is at the end of the path, Run tvs_b. You will need the full
path to find it, so carefully check your spelling as you write it down.á Complete the antispyware scan, exit the Microsoft Windows
Defender program and proceed to the next step.
b) Select the Run
item on the start menu.
c) Type regedt32 in the run dialog box and click OK.á
This launches the Registry Editor. Note: The regedt32 version of the registry
editor will allow you to modify the security of registry keys.á Never use the registry editor lightly; any
changes you make to registry keys are saved automatically.
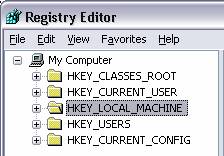
d) The left pane of the Registry Editor lists the key
hierarchy (similar to how the left pain of the windows explorer window displays a folder hierarchy):
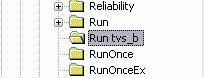
e) Use the registry path that you copied from the Microsoft Windows
Defender program as a guide and click the + buttons to expand the registry key hierarchy deeper until you
find the adware/spyware key.á From our
example registry key path above, it would look like the following illustration
once the key is selected.á Make sure your
offending adware/spyware key is selected just like this:
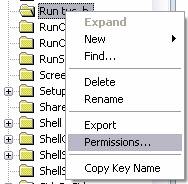
f)
Right click on
the key name and select Permissionsà on the context menu that pops down,
like this:
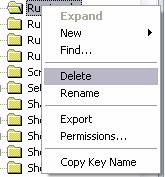
g) On the Permissions dialog click on the Advanced
button:
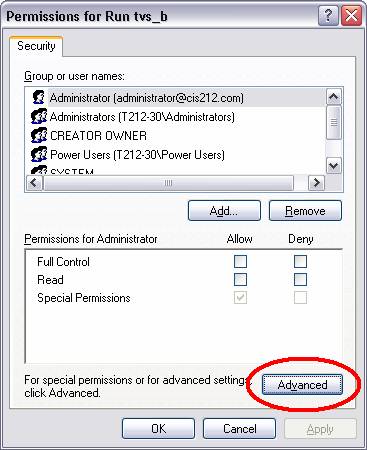
h)
Click on the Owner
tab of the Advanced
Security Settings dialog and then select the Administrators entry in the Change owner to
list box, as shown in the illustration below.á
Be sure to checkmark the Replace owner of subcontainers and objects option,
and click the OK
button.á Then click the OK
button on the Permissions
dialog to close it.
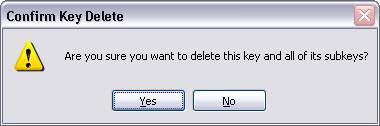
i)
Now that you
have changed the owner of the key to Administrator (which is you), right click on the
adware/spyware key name and select Delete:
j)
When the Confirm Key Delete
dialog appears, click on the Yes button to delete the adware/spyware key.
k)
Reboot your
computer and run do a full scan again with Microsoft Windows Defender.á Follow the step above for any other adware or
spyware registry key entries that keep coming back until the scan comes up
clean.
Installing and running the Lavasoft Ad-Aware program:
1. Open Internet Explorer and go to www.lavasoftusa.com/support/download.
2. Scroll down to the Ad-Aware SE Personal section. Click on the download link there.
3. Download and install the Ad-Aware SE Personal program, and run it.
4. Whenever you run Ad-Aware (which you should do at least once a week), you will need to update its adware definitions (like virus definitions for an antivirus program).á Do this by running Ad-Aware and clicking the Check for Updates Now link on the Ad-Aware window. Then click the Connect button on the next dialog that appears and install the new adware definitions file.
5. Now scan your computer with Ad-Aware by clicking on the Start button on the Ad-Aware window then click the Next button to begin scanning.
Important: You should scan your computer with the Microsoft Windows Defender and Ad-Aware applications at least once a week and anytime you suspect your system has been compromised.á
Recovering from a Browser Hijackùrecovery can be
difficult
Recovering from a browser
hijack can be one of the most difficult problems to solve.á The chance of success goes down drastically
the longer you wait to address the problem.á
If your computer was browser hijacked several weeks ago, and you ignored
it at that time and continued to use your browserùthough limited by the hijack,
the chances of recovering from the browser hijack now are practically
impossible.á On the other hand, if you
think your browser was just recently hijacked, following the steps below should
recover it.
╖
Applying a System Restore point to
recover a Browser Hijack
If the Browser Hijack Settings Restore feature
of the Microsoft
AntiSpyware tool does not solve your browser hijack issue, then we
must take more drastic measures.á Note: Applying
a system restore point will disable software you installed after the date the
system restore point was created. If you think your browser was hijacked
recently, then applying a system restore point from about a week ago will
likely not cause any problems. However, applying a system restore point from
over a month ago will disable any recently installed programs.á You will need to reinstall software that is
affected by applying a system restore point.
Recovering from a Browser
Hijack with a System
Restore
1. Click on the Start
button. Open the System Tools menu by opening All Programs, then Accessories,
and System
Tools. Then click on the System Restore item in System Tools.
2. On the System Restore dialog, click on the Restore my computer
to an earlier time option then click the Next button.
3. A calendar appears in the Select a Restore Point window.
Click a date on the calendar about a week prior to when you think your browser
was hijacked. Then click the Next
button and apply the restore point.
4. After reboot your computer try using your browser
again.á If your browser is still hijacked
precede to the next step.
╖
Recovering from a Browser Hijack manually or
doing a fresh install of Windows XP
If your browser was hijacked
several weeks ago and you didnÆt deal with it at that time, it is likely beyond
repair. You can attempt to recover your computer manually. Here is a link to a
popular tech forum thread that IÆve captured and stored here on this website.
In this thread several experts help a person recover their computer from a
particularly nasty browser hijack: Tech
Support Forum Thread.á The
manual recovery process is very
technical, but if you are not afraid to roll up your sleeves and venture into
techno-land you may be able glean enough information from this thread to
recovery your computer manually.
As a very last resort, doing a fresh install of the operating system may
be your only option. To do a fresh install of Windows XP, follow these steps:
1. Be sure to copy any files from your hard drive that
you want to save to floppy diskettes, CD ROMÆs, Zip disks or a
2. Once your important files are copied off your hard
drive, turn off your computer.
3. Locate your Windows XP CD and remove it from its case, turn
your computer on and immediately insert it into the CD ROM drive.á Watch the screen during the boot up process,
and when the message ôPress any key to
boot off the CD ROMö appears, press the spacebar to boot off of your Windows XP CD.
4. At the Welcome to Setup screen, choose the Setup Windows XP
Now option by pressing the enter key.
5. On the next screen, press the F8 key to agree to the license
agreement.
6. To install a fresh copy of Windows XP press the Esc key on the next screen.
7. At the next screen, press D to delete your hard drive
partition.á At the confirmation screen,
press Enter
to delete the partition.
8. At the next screen press C to create a new partition and use
all the available hard drive space.
9.
Continue
following the instructions to install Windows XP with the default options.
When the installation is
complete you will need to reinstall the applications you normally useùI know,
that sucks, but I did say this was the option of last resort. Very important:
While your computer is in this pristine state please follow the steps in the Preparing your Windows
XP Computer to Survive the InternetùStep by step article before you
start cruising the internet again to be sure your computer isnÆt vulnerable.
Back to main page
Revised: 04/24/2006